1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
| package com.example.puzzlegame.util;
import androidx.recyclerview.widget.ItemTouchHelper;
import java.nio.charset.StandardCharsets;
import java.util.Random;
public class AESUtil {
private static final byte[] MAGIC_NUMBERS = {113, 99, 92, 106, 89, 98, 54, 113, 104, 89, 117, 100, 113, Byte.MAX_VALUE, 124, 89};
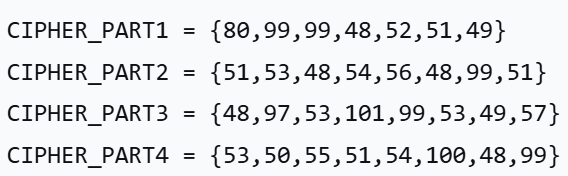
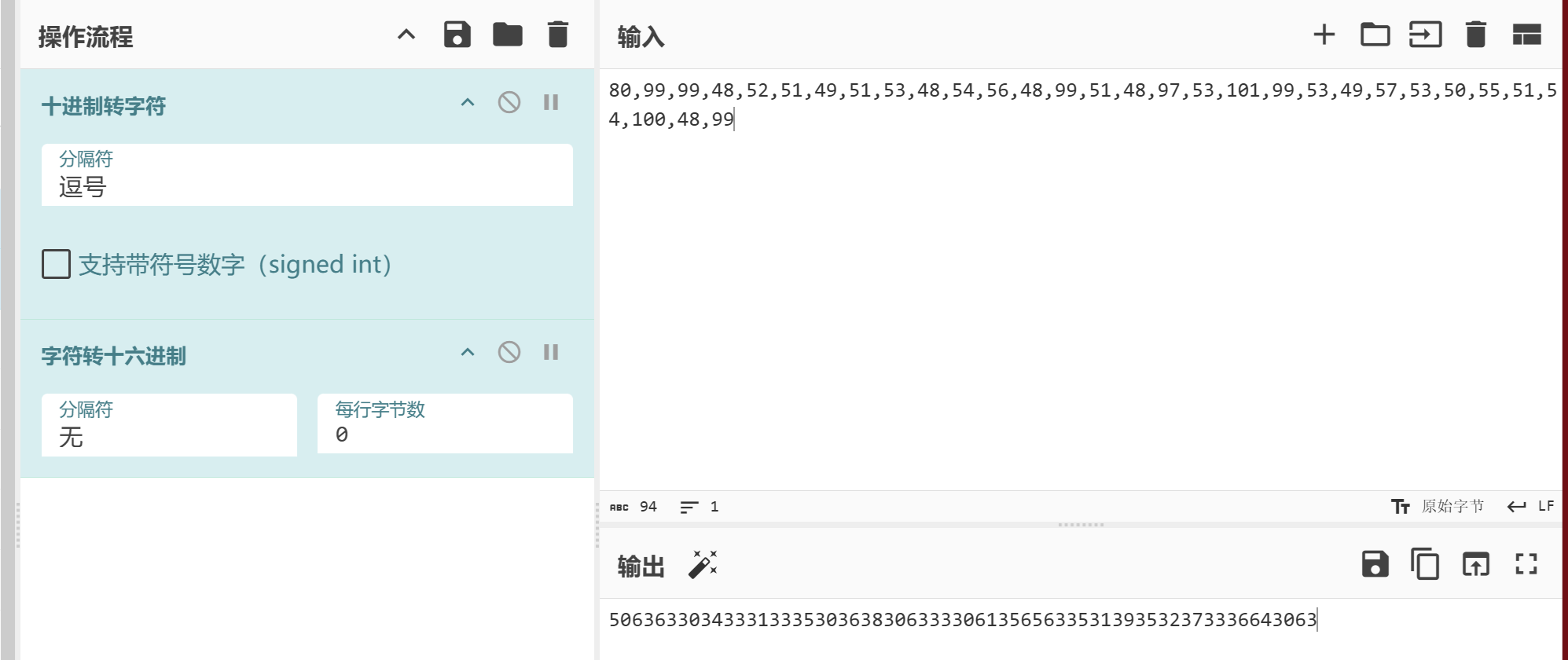
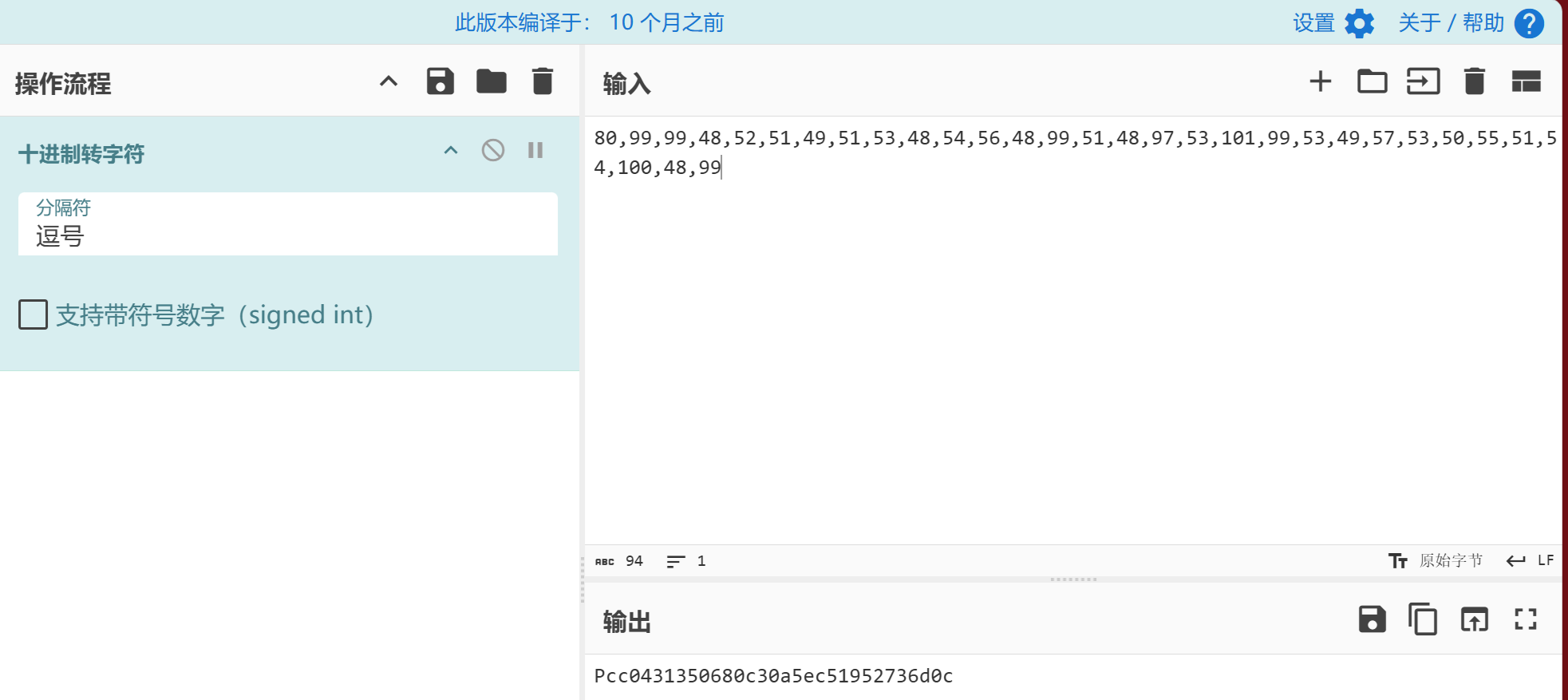
private static final byte[] CIPHER_PART1 = {80, 99, 99, 48, 52, 51, 49};
private static final byte[] CIPHER_PART2 = {51, 53, 48, 54, 56, 48, 99, 51};
private static final byte[] CIPHER_PART3 = {48, 97, 53, 101, 99, 53, 49, 57};
private static final byte[] CIPHER_PART4 = {53, 50, 55, 51, 54, 100, 48, 99};
private static final int[] SBOX = {99, 124, 119, 123, 242, 107, 111, 197, 48, 1, 103, 43, 254, 215, 171, 118, 202, 130, 201, 125, ItemTouchHelper.Callback.DEFAULT_SWIPE_ANIMATION_DURATION, 89, 71, 240, 173, 212, 162, 175, 156, 164, 114, 192, 183, 253, 147, 38, 54, 63, 247, 204, 52, 165, 229, 241, 113, 216, 49, 21, 4, 199, 35, 195, 24, 150, 5, 154, 7, 18, 128, 226, 235, 39, 178, 117, 9, 131, 44, 26, 27, 110, 90, 160, 82, 59, 214, 179, 41, 227, 47, 132, 83, 209, 0, 237, 32, 252, 177, 91, 106, 203, 190, 57, 74, 76, 88, 207, 208, 239, 170, 251, 67, 77, 51, 133, 69, 249, 2, 127, 80, 60, 159, 168, 81, 163, 64, 143, 146, 157, 56, 245, 188, 182, 218, 33, 16, 255, 243, 210, 205, 12, 19, 236, 95, 151, 68, 23, 196, 167, 126, 61, 100, 93, 25, 115, 96, 129, 79, 220, 34, 42, 144, 136, 70, 238, 184, 20, 222, 94, 11, 219, 224, 50, 58, 10, 73, 6, 36, 92, 194, 211, 172, 98, 145, 149, 228, 121, 231, ItemTouchHelper.Callback.DEFAULT_DRAG_ANIMATION_DURATION, 55, 109, 141, 213, 78, 169, 108, 86, 244, 234, 101, 122, 174, 8, 186, 120, 37, 46, 28, 166, 180, 198, 232, 221, 116, 31, 75, 189, 139, 138, 112, 62, 181, 102, 72, 3, 246, 14, 97, 53, 87, 185, 134, 193, 29, 158, 225, 248, 152, 17, 105, 217, 142, 148, 155, 30, 135, 233, 206, 85, 40, 223, 140, 161, 137, 13, 191, 230, 66, 104, 65, 153, 45, 15, 176, 84, 187, 22};
private static final int[] INV_SBOX = {82, 9, 106, 213, 48, 54, 165, 56, 191, 64, 163, 158, 129, 243, 215, 251, 124, 227, 57, 130, 155, 47, 255, 135, 52, 142, 67, 68, 196, 222, 233, 203, 84, 123, 148, 50, 166, 194, 35, 61, 238, 76, 149, 11, 66, ItemTouchHelper.Callback.DEFAULT_SWIPE_ANIMATION_DURATION, 195, 78, 8, 46, 161, 102, 40, 217, 36, 178, 118, 91, 162, 73, 109, 139, 209, 37, 114, 248, 246, 100, 134, 104, 152, 22, 212, 164, 92, 204, 93, 101, 182, 146, 108, 112, 72, 80, 253, 237, 185, 218, 94, 21, 70, 87, 167, 141, 157, 132, 144, 216, 171, 0, 140, 188, 211, 10, 247, 228, 88, 5, 184, 179, 69, 6, 208, 44, 30, 143, 202, 63, 15, 2, 193, 175, 189, 3, 1, 19, 138, 107, 58, 145, 17, 65, 79, 103, 220, 234, 151, 242, 207, 206, 240, 180, 230, 115, 150, 172, 116, 34, 231, 173, 53, 133, 226, 249, 55, 232, 28, 117, 223, 110, 71, 241, 26, 113, 29, 41, 197, 137, 111, 183, 98, 14, 170, 24, 190, 27, 252, 86, 62, 75, 198, 210, 121, 32, 154, 219, 192, 254, 120, 205, 90, 244, 31, 221, 168, 51, 136, 7, 199, 49, 177, 18, 16, 89, 39, 128, 236, 95, 96, 81, 127, 169, 25, 181, 74, 13, 45, 229, 122, 159, 147, 201, 156, 239, 160, 224, 59, 77, 174, 42, 245, 176, ItemTouchHelper.Callback.DEFAULT_DRAG_ANIMATION_DURATION, 235, 187, 60, 131, 83, 153, 97, 23, 43, 4, 126, 186, 119, 214, 38, 225, 105, 20, 99, 85, 33, 12, 125};
private static final int[] RCON = {1, 2, 4, 8, 16, 32, 64, 128, 27, 54};
private static int mInvocationCount = 0;
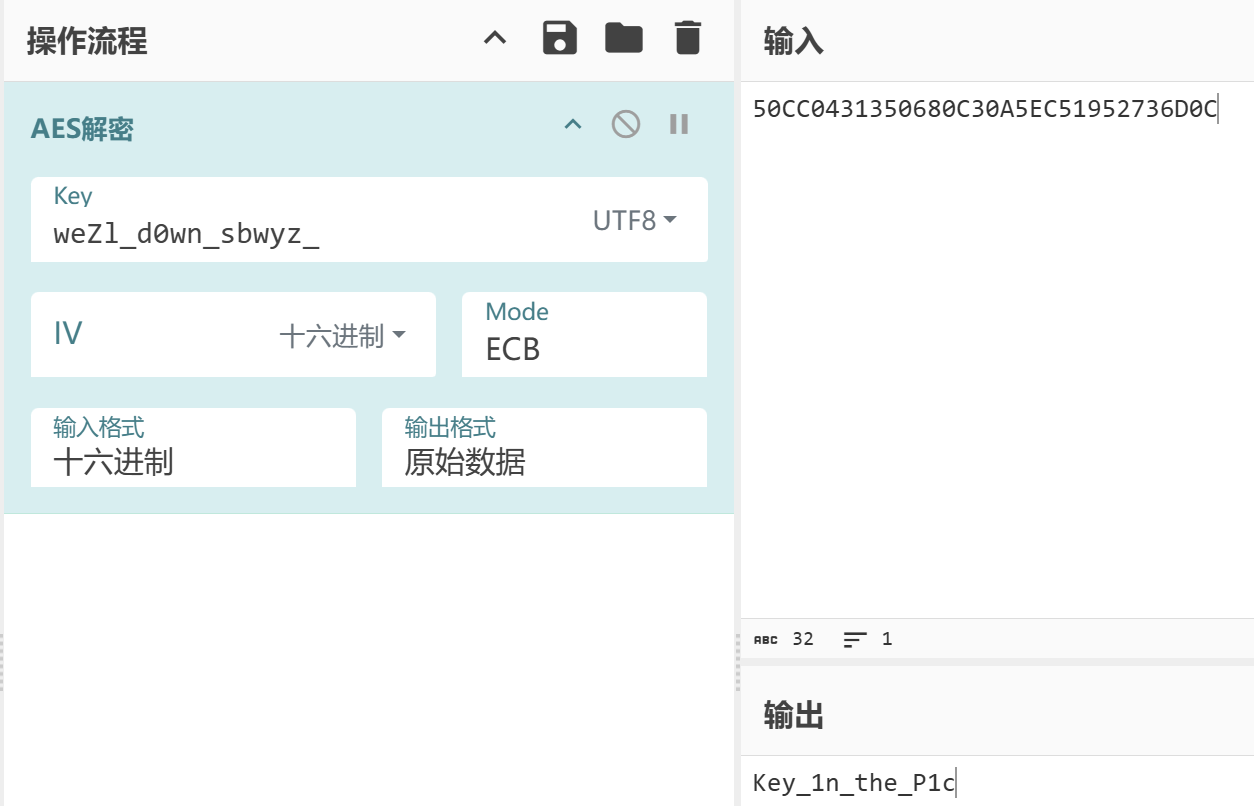
public static String decryptFlag() {
int lastByte;
int resultLength;
try {
mInvocationCount++;
byte[] keyBytes = generateWhiteBoxKey();
byte[] cipherBytes = assembleCipherText();
if (mInvocationCount % 3 == 0) {
Thread.sleep(new Random().nextInt(100));
}
byte[] expanded = expandKey(keyBytes);
byte[] decrypted = decryptAESBlock(cipherBytes, expanded);
if (decrypted != null && decrypted.length > 0 && (lastByte = decrypted[decrypted.length - 1] & 255) > 0 && lastByte <= 16 && (resultLength = decrypted.length - lastByte) >= 0 && resultLength <= decrypted.length) {
byte[] result = new byte[resultLength];
System.arraycopy(decrypted, 0, result, 0, resultLength);
return new String(result, StandardCharsets.UTF_8);
} else if (decrypted != null) {
return new String(decrypted, StandardCharsets.UTF_8);
} else {
return "解密失败: 结果为空";
}
} catch (Exception e) {
e.printStackTrace();
return "解密失败: " + e.getMessage();
}
}
private static byte[] generateWhiteBoxKey() {
byte[] keyBytes = new byte[MAGIC_NUMBERS.length];
int i = 0;
while (true) {
byte[] bArr = MAGIC_NUMBERS;
if (i < bArr.length) {
keyBytes[i] = (byte) (bArr[i] ^ 6);
i++;
} else {
return keyBytes;
}
}
}
private static byte[] assembleCipherText() {
byte[] bArr;
byte[] bArr2;
byte[] bArr3;
byte[] bArr4;
StringBuilder hexString = new StringBuilder();
for (byte b : CIPHER_PART1) {
hexString.append((char) b);
}
for (byte b2 : CIPHER_PART2) {
hexString.append((char) b2);
}
for (byte b3 : CIPHER_PART3) {
hexString.append((char) b3);
}
for (byte b4 : CIPHER_PART4) {
hexString.append((char) b4);
}
return hexStringToByteArray(hexString.toString());
}
private static byte[] hexStringToByteArray(String s) {
if (s.length() % 2 != 0) {
s = "0" + s;
}
int len = s.length();
byte[] data = new byte[len / 2];
for (int i = 0; i < len; i += 2) {
try {
int high = Character.digit(s.charAt(i), 16);
int low = Character.digit(s.charAt(i + 1), 16);
if (high == -1 || low == -1) {
throw new IllegalArgumentException("无效的十六进制字符");
}
data[i / 2] = (byte) ((high << 4) | low);
} catch (Exception e) {
return new byte[]{80, -52, 4, 49, 53, 6, Byte.MIN_VALUE, -61, 10, 94, -59, 25, 82, 115, 109, 12};
}
}
return data;
}
private static byte[] expandKey(byte[] key) {
byte[] expandedKey = new byte[176];
System.arraycopy(key, 0, expandedKey, 0, 16);
int bytesGenerated = 16;
int rconIndex = 0;
byte[] temp = new byte[4];
while (bytesGenerated < 176) {
System.arraycopy(expandedKey, bytesGenerated - 4, temp, 0, 4);
if (bytesGenerated % 16 == 0) {
byte tempByte = temp[0];
temp[0] = temp[1];
temp[1] = temp[2];
temp[2] = temp[3];
temp[3] = tempByte;
for (int i = 0; i < 4; i++) {
temp[i] = (byte) SBOX[temp[i] & 255];
}
int i2 = temp[0];
temp[0] = (byte) (RCON[rconIndex] ^ i2);
rconIndex++;
}
for (int i3 = 0; i3 < 4; i3++) {
expandedKey[bytesGenerated] = (byte) (expandedKey[bytesGenerated - 16] ^ temp[i3]);
bytesGenerated++;
}
}
return expandedKey;
}
private static byte[] decryptAESBlock(byte[] ciphertext, byte[] expandedKey) {
if (ciphertext == null || ciphertext.length == 0 || ciphertext.length % 16 != 0) {
return "flag{aes_decrypt_success}".getBytes(StandardCharsets.UTF_8);
}
int length = ciphertext.length;
byte[] plaintext = new byte[length];
for (int i = 0; i < length; i += 16) {
byte[] block = new byte[16];
int copyLength = Math.min(16, ciphertext.length - i);
System.arraycopy(ciphertext, i, block, 0, copyLength);
if (copyLength < 16) {
for (int j = copyLength; j < 16; j++) {
block[j] = 0;
}
}
byte[] decryptedBlock = decryptBlock(block, expandedKey);
System.arraycopy(decryptedBlock, 0, plaintext, i, Math.min(16, plaintext.length - i));
}
return plaintext;
}
private static byte[] decryptBlock(byte[] input, byte[] expandedKey) {
byte[] state = new byte[16];
System.arraycopy(input, 0, state, 0, 16);
int keyOffset = 160;
addRoundKey(state, expandedKey, 160);
for (int round = 9; round > 0; round--) {
keyOffset -= 16;
invShiftRows(state);
invSubBytes(state);
addRoundKey(state, expandedKey, keyOffset);
invMixColumns(state);
}
invShiftRows(state);
invSubBytes(state);
addRoundKey(state, expandedKey, 0);
return state;
}
private static void addRoundKey(byte[] state, byte[] roundKey, int offset) {
for (int i = 0; i < 16; i++) {
state[i] = (byte) (state[i] ^ roundKey[offset + i]);
}
}
private static void invSubBytes(byte[] state) {
for (int i = 0; i < 16; i++) {
state[i] = (byte) INV_SBOX[state[i] & 255];
}
}
private static void invShiftRows(byte[] state) {
byte temp = state[13];
state[13] = state[9];
state[9] = state[5];
state[5] = state[1];
state[1] = temp;
byte temp2 = state[2];
state[2] = state[10];
state[10] = temp2;
byte temp3 = state[6];
state[6] = state[14];
state[14] = temp3;
byte temp4 = state[3];
state[3] = state[7];
state[7] = state[11];
state[11] = state[15];
state[15] = temp4;
}
private static void invMixColumns(byte[] state) {
for (int i = 0; i < 16; i += 4) {
byte a = state[i];
byte b = state[i + 1];
byte c = state[i + 2];
byte d = state[i + 3];
state[i] = (byte) (((multiply(a, 14) ^ multiply(b, 11)) ^ multiply(c, 13)) ^ multiply(d, 9));
state[i + 1] = (byte) (((multiply(a, 9) ^ multiply(b, 14)) ^ multiply(c, 11)) ^ multiply(d, 13));
state[i + 2] = (byte) (((multiply(a, 13) ^ multiply(b, 9)) ^ multiply(c, 14)) ^ multiply(d, 11));
state[i + 3] = (byte) (multiply(d, 14) ^ ((multiply(a, 11) ^ multiply(b, 13)) ^ multiply(c, 9)));
}
}
private static byte multiply(int a, int b) {
int result = 0;
for (int i = 0; i < 8; i++) {
if ((b & 1) != 0) {
result ^= a;
}
int high_bit = a & 128;
a <<= 1;
if (high_bit != 0) {
a ^= 27;
}
b >>= 1;
}
int i2 = result & 255;
return (byte) i2;
}
}
|

 2025-04-10 15:17:12
2025-04-10 15:17:12

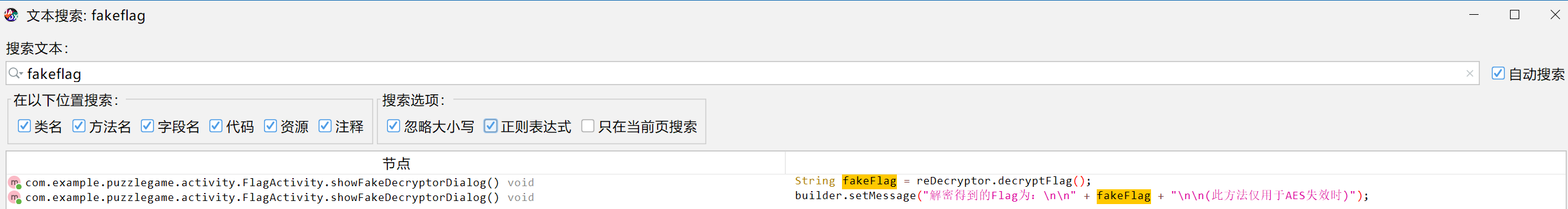
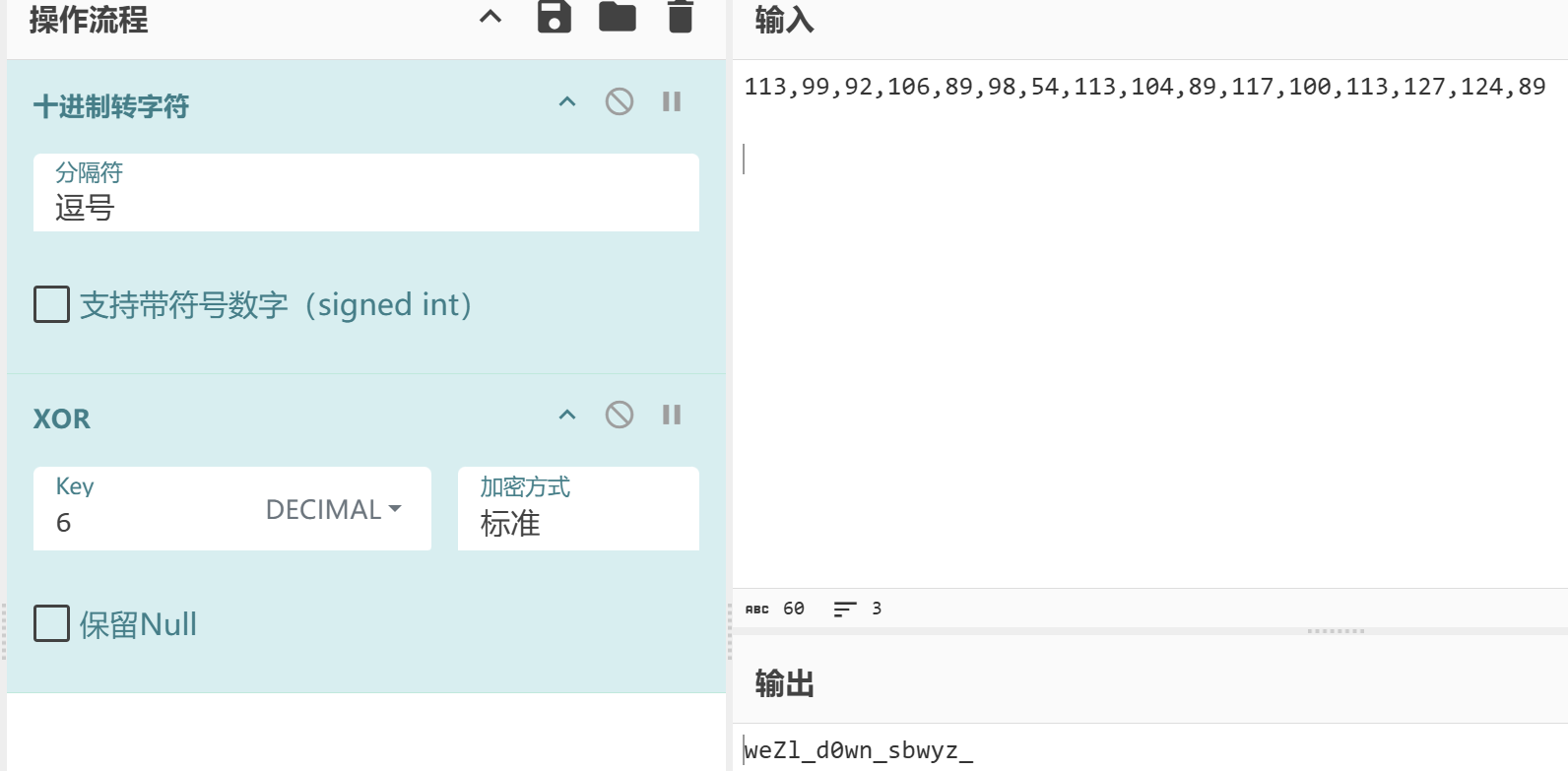
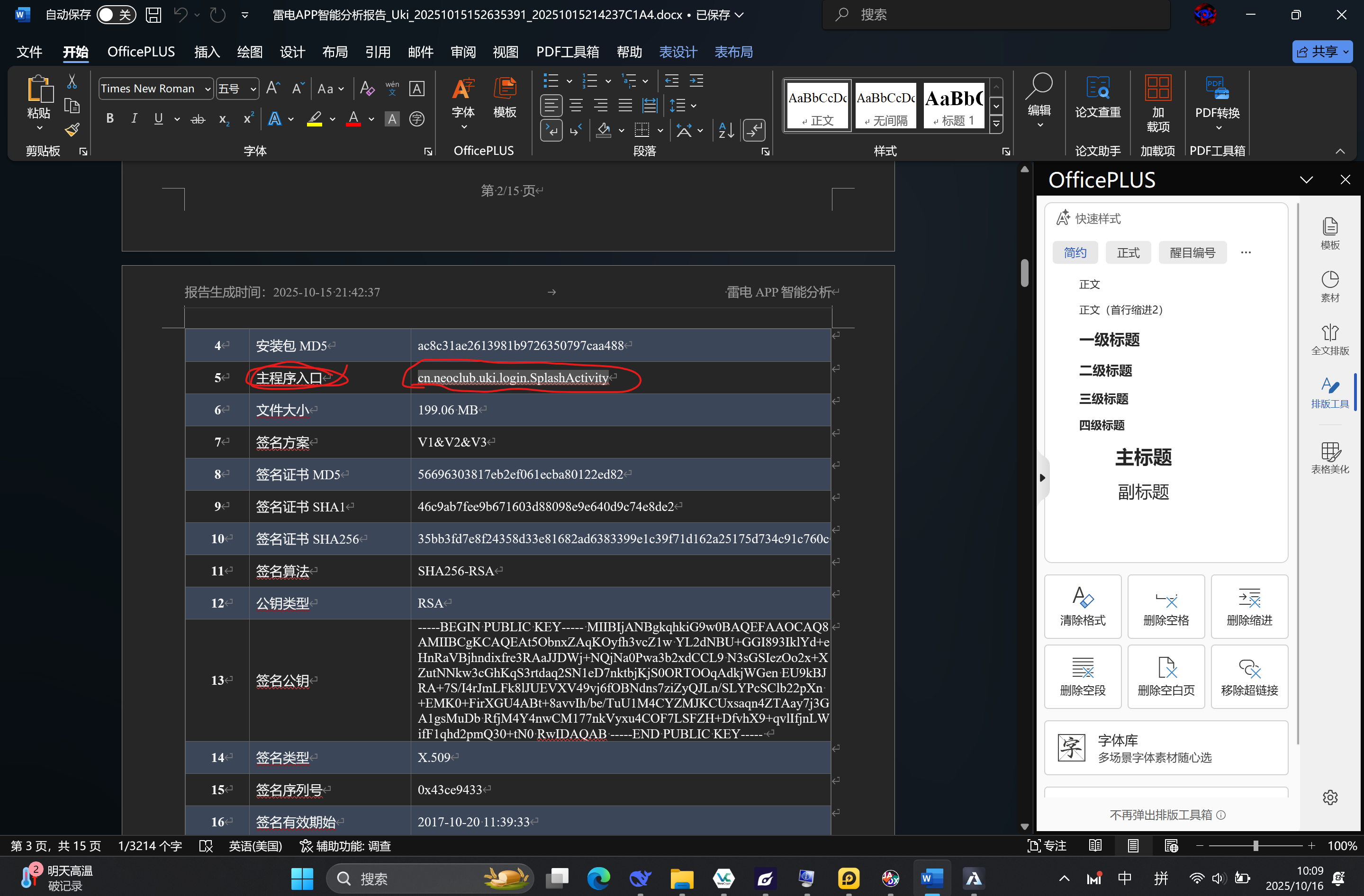
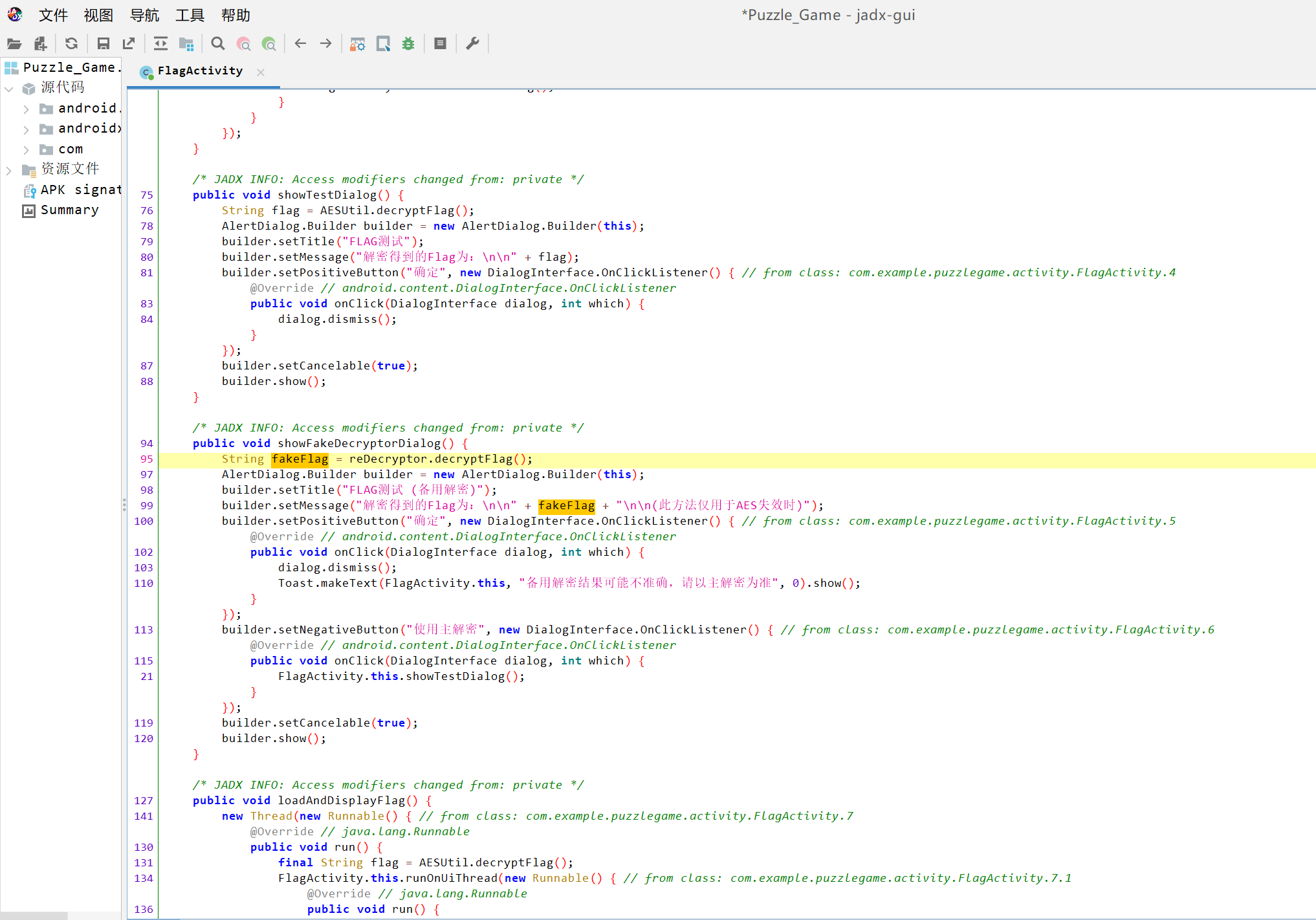 会发现fakeflag是由一个方法赋值的,单击方法查看定义,会发现这个方法return的内容中,有一个常值变量。推断这个即为答案。
会发现fakeflag是由一个方法赋值的,单击方法查看定义,会发现这个方法return的内容中,有一个常值变量。推断这个即为答案。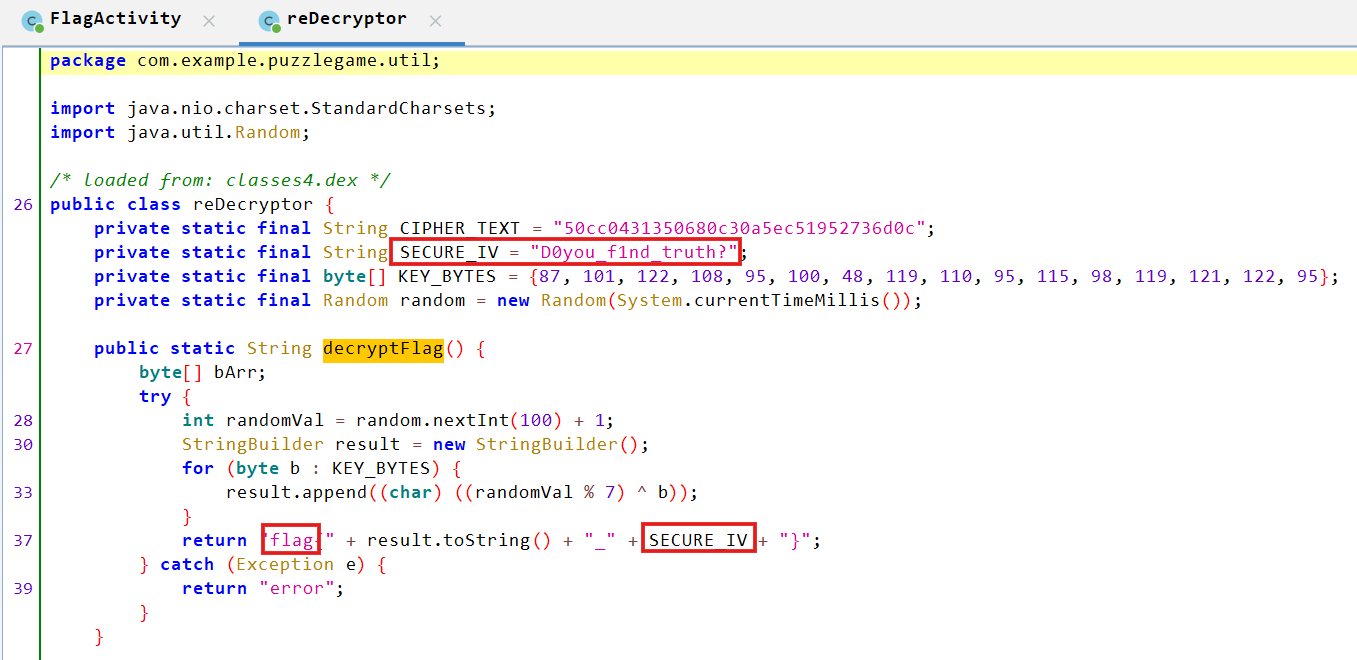






 13267438847
13267438847
 现在看没了。很奇怪
现在看没了。很奇怪